Open device management
Manage devices your way
We wanted an open-source MDM to easily use configuration-as-code, deliver the best possible experience for our employees, and make security happy.

Kenny Botelho
Lead Client Platform Engineer
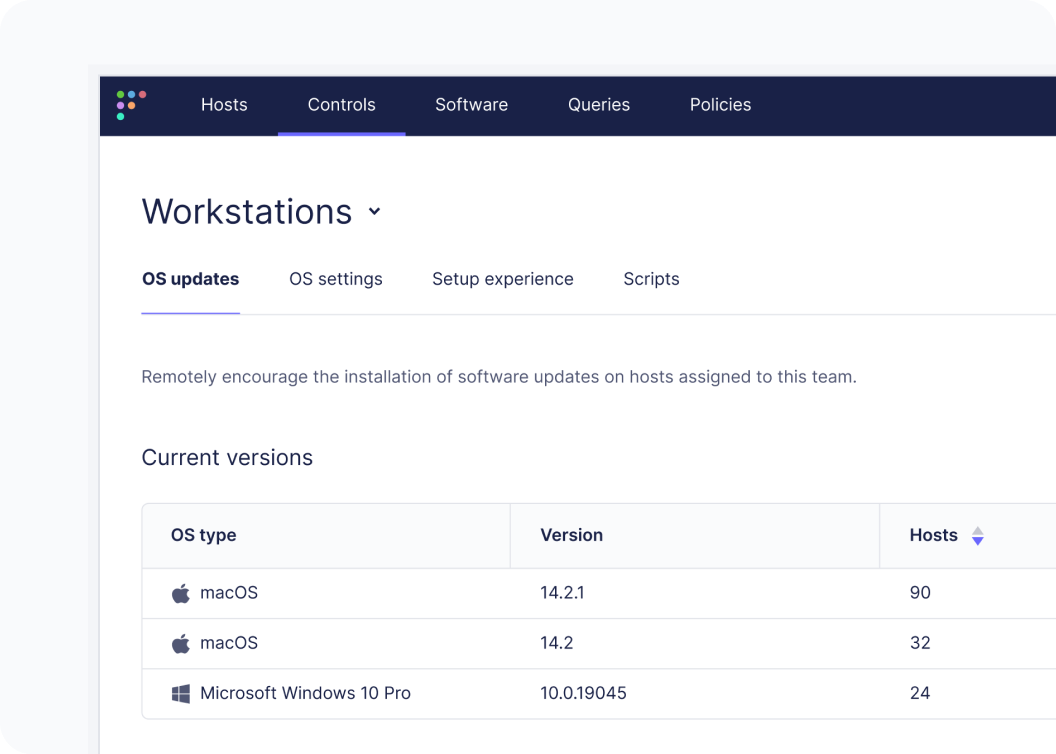
Operating systems
Manage Apple, Windows, Linux, and Android devices in one place. Fleet supports diverse, mixed environments with no vendor lock-in.
Automated enrollment
Drop ship devices with Apple Business Manager or Autopilot. End users can set up their own devices. No IT help needed.
Config management
Bring devices into a secure, predictable state, no matter where they start. Define, target, and deploy the right settings to the right devices.
Software management
Keep applications and plugins secure and up-to-date automatically. Install the software end users need or let them install it themselves via self service.
Custom scripts
Run the right script at the right time, across any platform. Remediate drift, gather diagnostics, and automate fleet-wide tasks.
Flexible by design
Manage devices via Fleet’s UI, API, or GitOps. The open-source community helps extend what’s possible, from platform support to deployment workflows.
Head-to-head with the big players
Considering a move to Fleet as a cross-platform, open-source MDM alternative? See how we compare:

Cloud or self-host with no restrictions
Cloud-only
On-prem only
On-prem discouraged
Zero-touch setup


Apple only
Windows only
iOS/iPadOS management
Community module
Complete device inventory ![]()



Mobile not supported
Operating system updates


Windows only
Apple only
Mobile not supported
Configuration management and scripting



Windows only
Apple only
Windows only scripting for app installs
Mobile not supported
Remote lock and wipe



Apple only
Windows only
No built-in Linux
App management



Windows only
Apple only
Mobile not supported
Automated device compliance



Windows only
Additional purchase
Mobile not supported
REST API
Intune or SCCM integration
Microsoft Graph API
Multiple APIs required
Config as code (GitOps)
Device reporting (<30 seconds) ![]()
6 hours
One-off scripts
Import / export
Interoperable
Windows only
Apple only
Proprietary
Open source
Free and paid version
Only free version
Compare with:

Cloud or self-host with no restrictions
Cloud-only
On-prem only
On-prem discouraged
Zero-touch setup


Windows only
Apple only
iOS/iPadOS management
Community module
Complete device inventory



Mobile not supported
Operating system updates


Apple only
Windows only
Mobile not supported
Configuration management and scripting



Apple only
Windows only
Windows only scripting for app installs
Mobile not supported
Remote lock and wipe



Apple only
No built-in Linux
Windows only
App management



Apple only
Windows only
Mobile not supported
Automated device compliance



Additional purchase
Windows only
Mobile not supported
REST API
Microsoft Graph API
Intune or SCCM integration
Multiple APIs required
Config as code (GitOps)
Device reporting (<30 mins)
6 Hours
One-off scripts
Import / export
Interoperable
Windows only
Apple only
Proprietary
Open source
Only free version
Shorten the feedback loop
Built for speed and transparency. No more waiting for closed systems to catch up.
Get near-instant visibility into your Apple, Linux, and Windows devices from a single, open platform.
Verify changes in real time with full audit logs.
Confidently resolve issues before users notice.

Deploy anywhere you want
On-prem, cloud, or air-gapped. Fleet works where you need it. No lock-in or black boxes. Fleet adapts as you grow.
No hidden dependencies or forced cloud services.
Flexible APIs and open data formats.
Keep control of your infrastructure and your data.
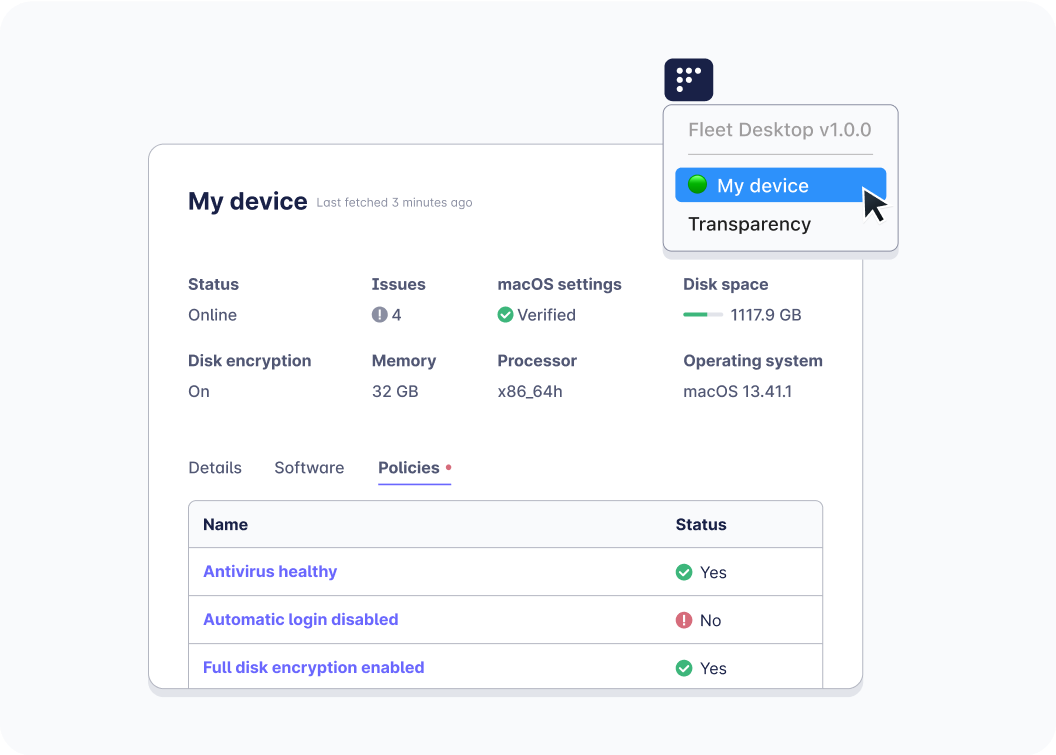
Scope transparency
Increase buy-in from end users by clarifying how their devices are managed.
Give end users assurance about what actions IT can take on their computer.
Let end users see exactly what data is collected, all the way down to the source code
Set clear expectations about how to configure company devices
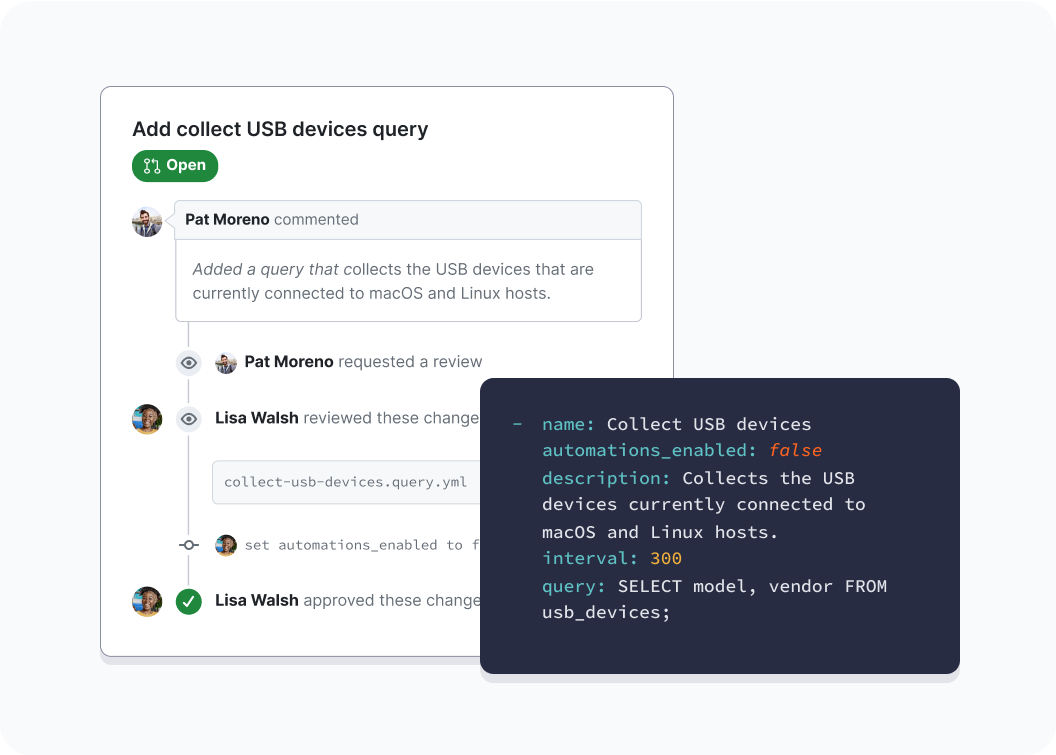
Modern change management
Provide a transparent log of all changes and collaborate on how your devices are managed.
Democratize change with GitOps so everyone can contribute to device management and security.
Maintain reliable employee experiences with version-controlled changes and enhancements.
Use CI/CD and peer reviews to look before you leap. (Configurable)